Your credentials may already be exposed. Check it now.
The biggest credential leaks aren't the ones making headlines.
Stealed detects what others miss: infostealer logs, stealthy theft, successful phishing.
Your data belongs to you,
keep it that way.
Get alerted as soon as a leak is detected, directly on your favorite platforms.
The threat is real. Numbers don't lie.
Attackers no longer need advanced techniques. A single stolen credential is enough to breach your systems, without triggering a single alarm.
of attacks on exposed assets start with stolen credentials
of stolen credentials in 2024 come from infostealers
passwords stolen by infostealers in 2024
attacks per company every week
From leak to action in minutes
Collection
Continuous scan of 500+ sources
Analysis
Real-time indexing
Detection
Automatic matching
Action
Alerts and remediation
What data?
We analyze two complementary source types for maximum coverage.
Infostealers
Logs from silent malware that exfiltrate sensitive data from infected machines.
Combo Lists
Massive compilations of credentials from multiple sources.
Features built for action
Monitor, analyze and respond to credential leaks in real-time.
Two complementary perspectives
Analyze your leak data from two angles for complete coverage.
Internal Insight
Monitor leaks related to your domain emails. Identify which employees are exposed and on which sites their credentials were compromised.
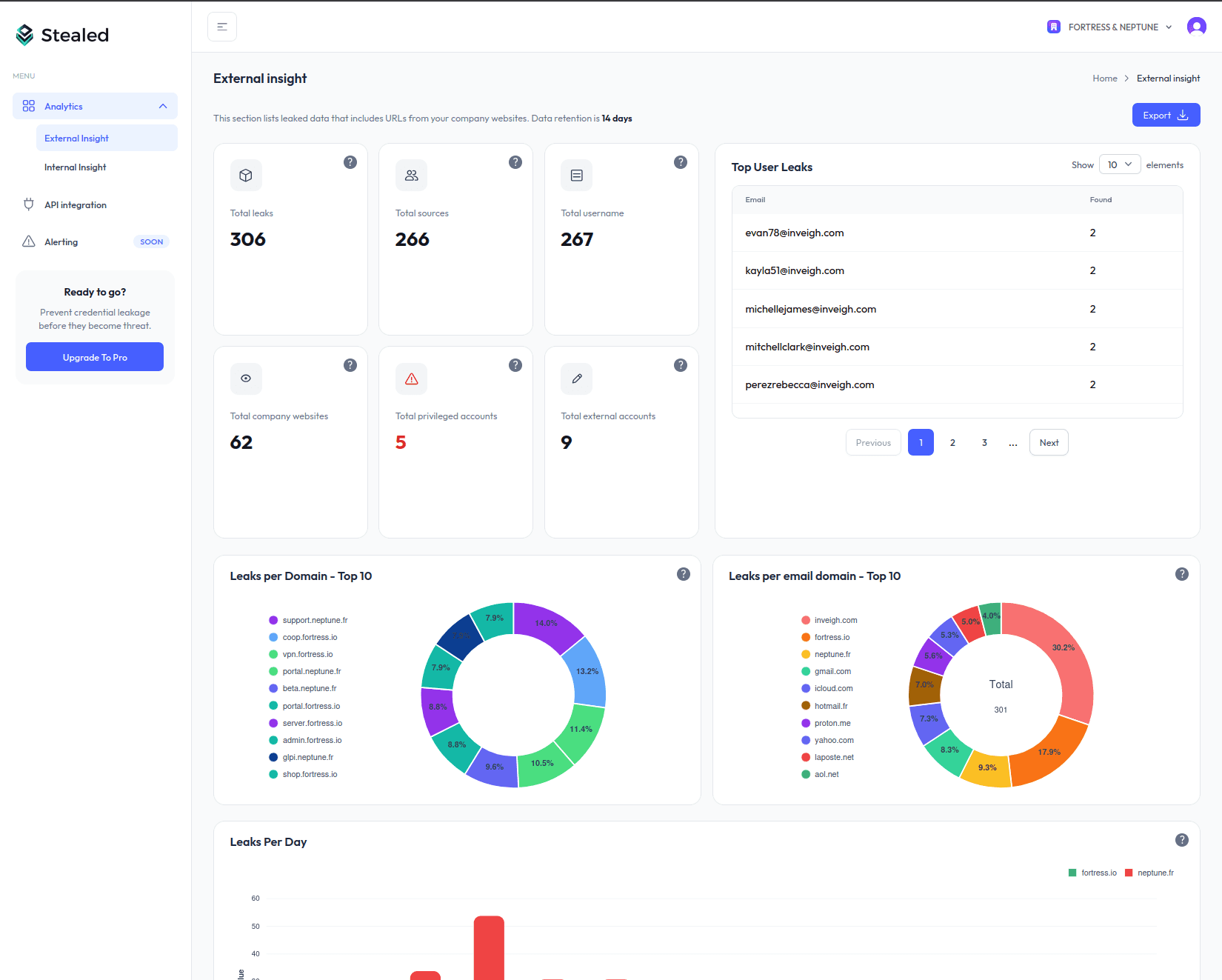
External Insight
Monitor third-party sites where your users connect. Detect when your services are targeted by attackers.
Analytics & Dashboard
Overview of your perimeter: leaks per domain, impacted emails, leak types, trends over time.
Details & Search
Access complete information: username, masked password, connected site, detection date. Filter and search through your data.
Pattern Tracking & Alerts
Configure patterns to monitor, historize data, add comments for incident tracking. Real-time alerts on all your channels.
REST API
Access all your data via our API. Integrate Stealed with your SIEM, SOAR or internal workflows.
const response = await fetch(
'https://api.stealed.io/v1/leaks',
{
headers: {
'Authorization': `Bearer ${API_KEY}`
}
}
);Who is it for?
Stealed adapts to your monitoring challenges.
MSP / MSSP
- Prospect with a free security audit
- Add a CTI layer to your offerings
- Manage all clients from a single dashboard
SaaS
- Alert users when their account is compromised
- API integration in a few lines of code
- Zero manual work, fully automated
SMBs
- Ready in 5 min, no expertise required
- Monitor your emails and domain names
- Get only the alerts that matter
Enterprise
- Consolidated view across all subsidiaries
- Native SIEM/SOAR integration
- Risk scoring to prioritize your incidents
What security teams are saying
The API was integrated into our stack in less than a day. We now offer credential monitoring to our clients as an add-on service.
Clean interface, setup in 30 minutes. We monitor our domains without needing a dedicated security team.
We monitor 12 subsidiaries from a single dashboard. Subdomain granularity lets us pinpoint exactly which entity is exposed.
The data is fresh and actionable. We detected compromised client credentials before they even knew about it.
Integrated with our SIEM in a few hours. Webhooks allow us to automate incident response directly.
We monitor emails of our lawyers and sensitive clients. The tool is simple, alerts are precise.
The API was integrated into our stack in less than a day. We now offer credential monitoring to our clients as an add-on service.
Clean interface, setup in 30 minutes. We monitor our domains without needing a dedicated security team.
We monitor 12 subsidiaries from a single dashboard. Subdomain granularity lets us pinpoint exactly which entity is exposed.
The data is fresh and actionable. We detected compromised client credentials before they even knew about it.
Integrated with our SIEM in a few hours. Webhooks allow us to automate incident response directly.
We monitor emails of our lawyers and sensitive clients. The tool is simple, alerts are precise.
A plan for every need
Start free, scale as you grow. Unlimited email monitoring on all plans.
Free
Individuals
Perfect to discover Stealed and get an overview.
- 1 monitored subdomain
- 1 user
- Unlimited emails
- 7-day retention
- Statistics only
- Email alerts
Starter
SMBs / Freelancers
For freelancers and small businesses monitoring their domain.
Billed annually
- 3 subdomains
- 1 user
- Unlimited emails
- 14-day retention
- Access to leak data
- Email alerts
- Email support
Pro
SMBs / Mid-market
For SMBs and security teams looking to automate.
Billed annually
- Unlimited subdomains
- 5 users
- Unlimited emails
- 30-day retention
- Advanced analysis module
- API & Webhooks
- Reports & exports
- Priority support
Enterprise
Enterprise / MSSP
For large organizations, MSSPs and specific needs.
Contact us for custom pricing
- Unlimited domains
- Unlimited subdomains
- Unlimited users
- Custom retention
- Unlimited API
- Multi-tenant (MSSP)
- SIEM/SOAR integrations
- Dedicated support & SLA
- Custom onboarding
Questions? Check our FAQ
Frequently Asked Questions
Find the most common questions about Stealed and how to use it.
Contact
Still haven't found what you're looking for?
Feel free to contact us, we'll respond within 48 hours.
Response time
Within 48 hours